How to Draw Your First Data Map

From Treasure Island to The Gold Bug, we know a treasure map as an old hand-drawn document containing arcane clues for the characters to follow. X marks the spot. Aaargh! In the privacy world, our treasure map is a data map.
Data mapping shows how data from one information system maps to data from other systems. A data map is a legal requirement, but it’s also the most effective way to understand the risks inherent to serial disclosure and transfer of data.
At xMatters, client data flows serve multiple purposes and are always kept up to date. Managing data maps complies with GDPR or CCPA, and it’s key to maintaining a superior data incident response plan. Maps are also valuable when you have an information security system based on a risk management approach. If you know exactly where the data is coming from and where it’s going, it’s easier to mitigate any vulnerabilities that might arise in the flow.
In a 2020 research study by the Identity Defined Research Alliance, only 26% of IT security and identity professionals said they were “very confident” in their companies’ overall ability to effectively manage and secure all types of identities. And you can see why: organization are trying to comply with an alarming number of regulations, which is causing them to seek help by purchasing security solutions.

Many companies are complying with up to five privacy laws.
Source: IAPP, 2019
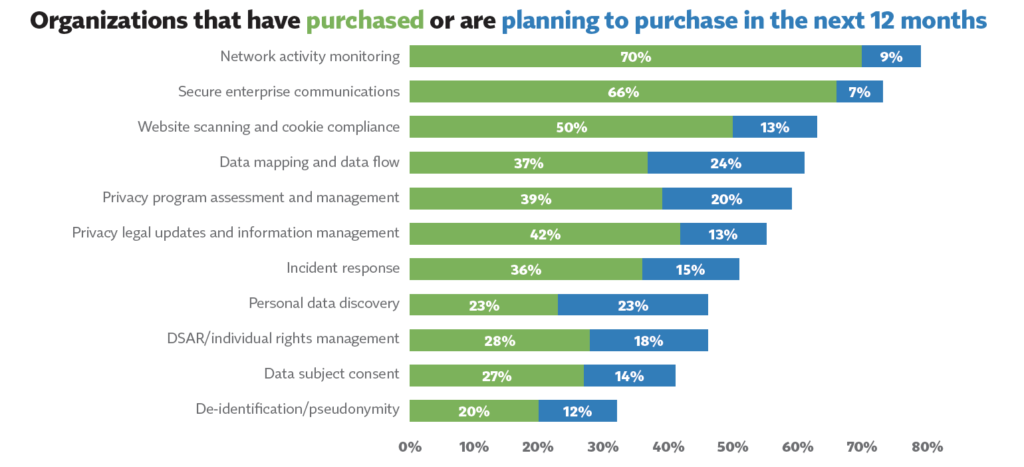
A high percentage of companies have already purchased a security product.
Source: IAPP
Drawing Your First Data Map
Drawing your first map will be easier if you follow the steps below:
- Choose the right approach for your organization: You may choose to produce whole data maps all at once, or you may decide to piecemeal a data map for each team, service, or department at a time.
- Document the process and review it at least annually: Maintain a documented process for developing and maintaining your data map so you can compare and control mapping activities. Automate parts of the data mapping process if you can.
- Maintain an inventory of all software your company uses: Before drawing a map, you need to know which applications are used internally, what types of data are processed in each one, and who in the company owns each software.
- Create specific data maps based on data types: Classify data based on type, sensitivity, or value, according to cybersecurity company Imperva. Mapping and analytics platform ArcGIS Document the principles for classification. Developing specific data maps to accommodate different requirements is the most effective way to visualize the necessary controls for that data type.
- Use data maps as supporting documents to optimize data incident plans: If you understand the flow of your clients’ data, you can prioritize and contain incidents more efficiently.
- Stay up to date: Periodically review any updates and publications by the data privacy authorities, such as the UK-ICO.
One of the most important parts of the process is understanding your specific privacy requirements, including cross-border data transfers across countries or other economic regions. Align each data map with the applicable privacy regulations, and you will better accommodate specific processes and be more efficient when responding to an incident.
Data maps are a valuable tool for any business. Make them dynamic, decisive, and easy to read. Give management a powerful document to support decisions and better protect client and organizational data.

