Risk Management In DevOps: How to Put Software Development Security First
DevOps risk management aims to identify and address potential risks early in the Software Development Life Cycle (SDLC) while ensuring agility and efficiency.
Building software development security into the early stages of product development is critical. If ignored, this increases vulnerabilities, raises costs, and impacts time to market for new products.
The misconception that security slows innovation often stems from improperly integrating security processes. By embedding security into DevOps workflows—commonly called DevSecOps—organizations can achieve continuous delivery while minimizing risks and maximizing software quality.
So, what are the keys to building software development security in the early stages of product development? What are the costs of ignoring security? And what are the best DevOps tools for risk mitigation? In this article, we’ll explore these answers and more.

Speed, quality, and cost in product development. Image source: https://m.subbu.org/cloud-optimization-circus-65f3b47d0c79
Risk Identification In DevOps & Why You Should Invest In DevSecOps
Building software development security right into the product delivery process through automated build processes is frequently called DevSecOps.
This term combines DevOps and Security, reflecting the DevOps principle of continuous improvement and delivery through containerization. It also includes testing security compliance targets with each code commit, in addition to testing against performance and deployability metrics.
The benefits of testing early and often are well documented. Fixing production issues can cost up to five times more than addressing them during development. According to the Consortium for Information & Software Quality (CISQ), poor software quality in the United States cost US companies over $2.41 trillion in 2022 alone.
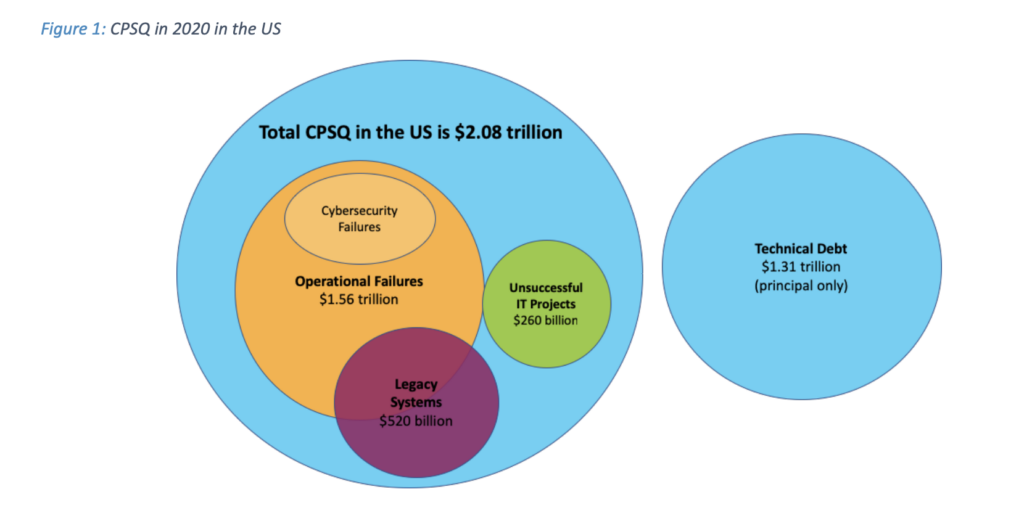
Total CPSQ in 2020 in the United States of America. Image source: https://www.it-cisq.org/cisq-files/pdf/CPSQ-2020-report.pdf
By integrating risk management into each phase of the DevOps pipeline, teams can proactively address challenges that could lead to costly failures or breaches.
Best Tools For Risk Identification and Mitigation
Identifying risks early requires leveraging tools and toolchains that align with DevOps workflows.
DevOps & SRE Incident Management Solutions xMatters empowers teams to automate workflows, ensuring seamless incident management, with the following tools:
-
- Incident Response Software: Automates resolutions, reducing downtime and manual effort.
- Incident Management Analytics: Offers valuable insights into performance metrics.
- IT Alerting Software: Filters alerts and ensures relevant team members receive actionable notifications.
- Integrations: Resolve incidents quickly with tool integrations like GitLab.
DevOps Risk Mitigation Strategies
Effectively mitigating risks in DevOps requires combining tools, cultural shifts, and strategic thinking. Here’s how organizations can achieve this:
Strategy 1: Enabling Better CI/CD Processes
Scanning code for vulnerabilities as part of the build-test-deploy pipeline is a critical enabler for CI/CD processes. Continuous, automated security scanning is essential because development teams could never comb through every line of code or every change set. Here’s why:
Modern applications typically rely on open-source libraries, which depend on other third-party dependencies. These chains of dependencies constitute a complex web of code owned and maintained by disparate teams distributed worldwide who are often unaware of each other’s existence or how they use code.
Neglect security scanning at your own risk. Popular package repositories like NPM have been attacked, leaving developers at the mercy of repository owners (either hijacked or otherwise).
Fortunately, we have tools to help with this, including open-source tools like UpGreat, which make it easy to ensure that complex chains of dependencies are up to date.
Strategy 2: Building A Strong Company Culture
Tools alone do not make a top-performing product development team; it’s also about company culture and collaboration. According to Software Security Culture in Development Teams: An Empirical Study, a culture of standards compliance, in combination with structured guidelines and established values, is necessary for securing success.
Encourage strong communication and collaboration between development, operations, and security teams. An influential culture can make the best possible decisions early in the software delivery process.
No scan is perfect. At xMatters, we apply the scientific method to identify real threats from the red herrings, but there is still an art to it.
This is especially true for native mobile apps. Native apps typically follow a different release cadence than web apps because they need to be updated on the device instead of simply refreshing a webpage. They also go through a more involved review process with Apple and Google. The code is much more complex for potential hackers to inspect, and apps can be designed with greater control over their runtime operation.
At xMatters, we integrate continuous Static Application Security Testing with various tools and services. We build vulnerability scanning into every commit through automated processes, which saves us time.
Strategy 3: Use Common Sense When Automating
Leverage automated tools to conduct continuous security scans, code reviews, and penetration tests. Techniques like Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) help ensure your applications and infrastructure remain secure without adding delays to your CI/CD pipelines.
Relying entirely on automation without human review can lead to critical issues going undetected or unnecessary delays caused by overstated risks. Leave low-priority tasks or processes requiring creative problem-solving to manual intervention, where human expertise truly shines.
Strategy 4: Adopt a Shift-Left Approach
Move risk identification and mitigation to the earliest stages of the DevOps lifecycle by embedding security, compliance, and quality checks into the development phase. For example, using static code analysis tools during coding helps detect vulnerabilities before they progress further in the pipeline.
Traditionally, QA and security teams were often involved only after development was complete. By shifting-left, these teams collaborate with developers during the design phase to review potential risks in architecture or feature plans.
A shift-left approach also promotes a culture of security awareness among developers, encouraging them to take responsibility for the code they write. By integrating security practices into their day-to-day work, developers can become more proactive in identifying and addressing potential risks.
DevOps Risk Management Made Easy With Everbridge xMatters
DevOps risk management is essential for maintaining security without sacrificing speed or quality. Strategies like early testing, automated processes, and fostering a solid company culture help organizations mitigate vulnerabilities while optimizing workflows.
xMatters stands out as a leader in DevOps and DevSecOps, offering cutting-edge tools like incident management software and automated workflows to enhance risk management.
To transform your organization’s approach to DevOps risk management, request a demo and explore how xMatters can support your journey.
FAQs Related To DevOps Risk Management
What is risk management in DevOps?
DevOps risk management involves identifying, assessing, and mitigating security vulnerabilities and operational risks throughout the software development and delivery lifecycle.
What are the 5 risk management approaches?
The five primary approaches are risk avoidance, mitigation, transfer, acceptance, and monitoring. These strategies help organizations effectively tailor responses to different types of risks.
